On Strong Identity Management
Alice wants to send an encrypted message to Bob; she knows his address, but doesn’t know the public key that goes with that address. Using GPG, Alice would look up his address on a key server, the issue is of course that anyone can upload a key associated with Bob’s address.
Using the “web of trust” model, Alice would look at the different keys and see which ones are signed, and if any of them are signed by people she knows. The problem is that Alice doesn’t normally use GPG, and she hasn’t marked the keys of the people she knows as trusted (I expect this is true for most casual GPG users), thus, she can’t tell what key is signed by keys she should trust, versus the ones signed by keys she shouldn’t.
Read more…Jumping through hoops…
There are two ways to implement security:
- Real security, based on empirical evidence and analysis.
- Checklist security, based on the latest checklist somebody says is important.
When security is based on real evidence and analysis, policies are enacted based on real gain and measured against the business impact. Risks are considered, and the costs versus benefits are well understood so that policy choices are based on real, useful information.
On the other hand there’s security by checklist. Costs aren’t calculated, risks aren’t understood, business impacts are ignored. All that matters is that somebody gets to check a box on a form; there’s no understanding, no logic, and likely no real benefits involved.
Read more…SMIMP - The Design Goals
Originally posted on SMIMP.org
As we work to get everything tightened up for the first public draft, I wanted to share some more details about just what it is we are working on. I’d love to go ahead and release a public draft today - but the specification needs to be solid. To avoid having too many distractions about half-baked parts of the specification, we are waiting till it’s a bit more solid (or the end of the month, which ever comes first).
Read more…Introducing SMIMP
Originally posted on SMIMP.org
I’m Adam Caudill, the primary author of the soon to be released SMIMP specification. SMIMP was born out of a series of conversations about email, and the pain around email security; those that have worked on this project share a common belief:
Email, as we know it today is fatally flawed. Any attempt to fix the security issues will simply add complexity and increase the attack surface. For an email-like system to achieve the security and privacy goals that the modern world requires, the protocol itself must be designed with security in mind, with each and every decision made. Here, the authors of email failed, SMIMP was created to start a meaningful conversation about how to correct their mistakes.
Read more…The Sinking Ship of E-Mail Security
E-Mail, the venerable old standard for internet text messages, dating back to the early 1980s – and back to the early 1970s in other forms, has long been the “killer app” of the internet. While so many companies try to make the next great thing that’ll capture users around the world – none of these compare to the success of e-mail. It is likely the single most entrenched application-layer protocol used today.
Read more…phpMyID: Fixing Abandoned OSS Software
phpMyID is a simple solution for those that want to run their own OpenID endpoint – the problem is that its author stopped maintaining the project in 2008. Despite this, there’s still quite a few people that use it, because it’s the easiest single-user OpenID option available.
Unfortunately, the author didn’t follow best practices when building the software, and as a result multiple security flaws were introduced. In 2008, a XSS was identified and never fixed (CVE-2008-4730), in the years since then it seems the software has been below the radar. While conducting a pentest I discovered a previously undocumented XSS (CVE-2014-2890) – which left me with a dilemma – what to do about it?
Read more…Security By Buzzword – Why I don’t support Ensafer
Update: I had a call with Ensafer’s CTO, Trygve Hardersen to discuss the issues I brought up, and what they can do about it. First, they updated the site so that downloads are now over HTTPS. He stated that the infrastructure that powers their service is separate from the website, and everything is over HTTPS. They are working on making documentation available, and hope to have the first documents available soon. Once I get a chance to look over their documentation, I’ll post further updates.
Read more…HTTP Considered Harmful – The Need For Negative Feedback
We all know, and well understand what this means when we see it in a browser:
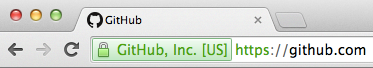
It means that the connection is encrypted, and that some degree of validation has occurred to verify that the server is who it claims to be. Through the years, users have been taught to trust sites when they see that, or the all too familiar ’lock’ icon – when users see it, they assume their data is safe.
Read more…On Opportunistic Encryption
Opportunistic encryption has become quite a hot topic recently, and blew up in a big way thanks to an Internet Draft that was published on February 14th for what amounts to sanctioned man-in-the-middle. Privacy advocates were quickly up in arms – but it’s not that simple (see here). As pointed out by Brad Hill, this isn’t about HTTPS traffic, but HTTP traffic using unauthenticated TLS; thanks to poor wording in the document, it’s easy to miss that fact if you just skim it.
Read more…Evernote for Windows, Arbitrary File Download via Update
Update: The Evernote security has reported that this issue is resolved.
Evernote for Windows downloads its update information via HTTP, making it subject to man-in-the-middle attacks – further, this allows an attacker to specify an arbitrary file for the updater to download. The good news is that Evernote will not execute the file thanks to signature validation – but the file isn’t removed, so it’s available for later use.
As the file isn’t executed, it isn’t a critical issue.
Read more…